
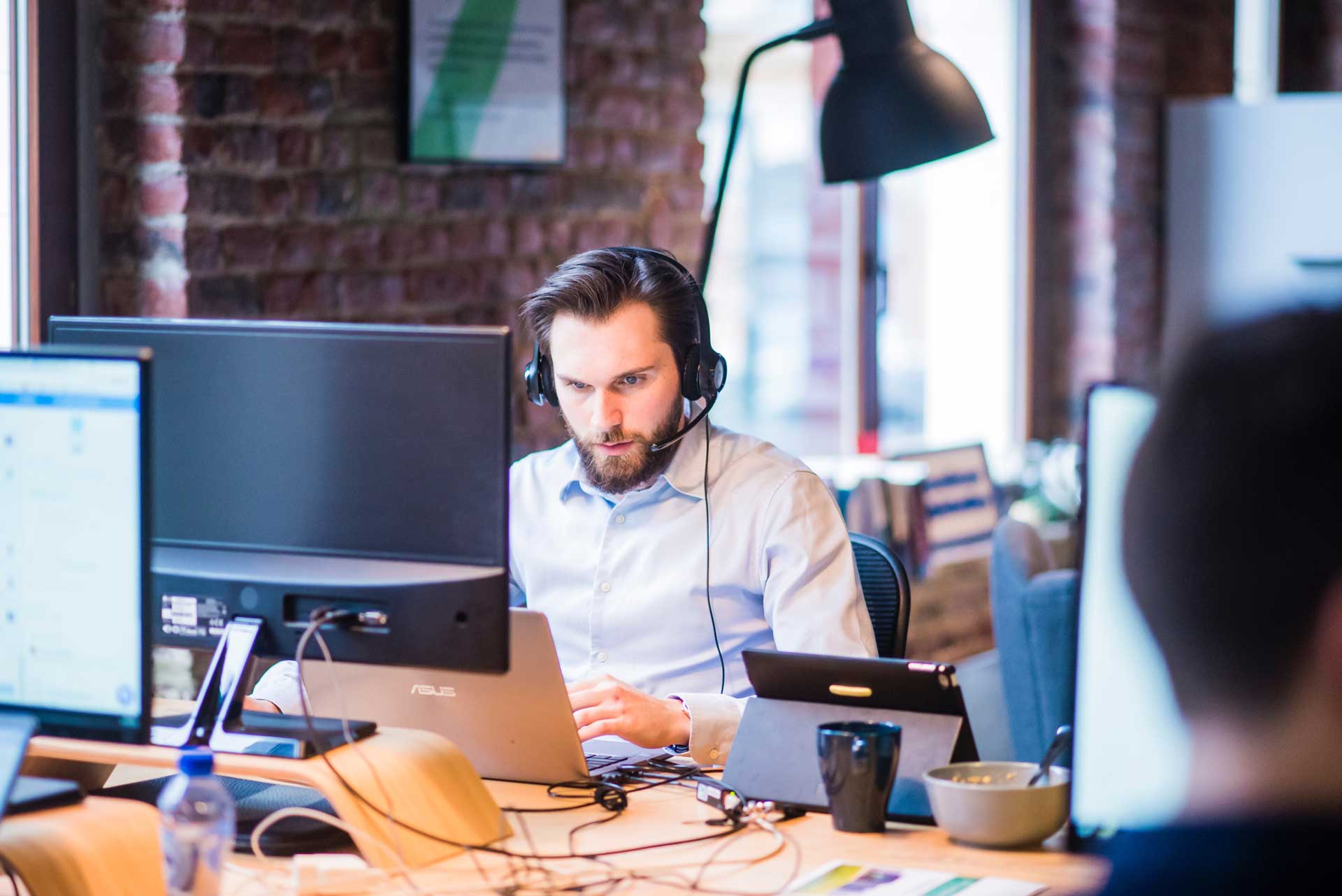
Enabling Remote Workers With Technology
How to Keep Business Operations Rolling Without Compromising Productivity or Security
It's a challenge to keep business operations rolling during a crisis situation. It’s even tougher when the situation requires that staff work remotely, especially if you’re not used to working that way. How do you maintain productivity and security while providing the flexibility that employees need to get their work done at home, or any other location for that matter?
The key to building an efficient, productive remote workforce is technology, and thanks to major advancements in technology, remote work has evolved. Before you send everyone home with laptops and open the ports on your firewall so that they can remote in, get informed about the right way to enable workers with technology.
Goals for Enabling Remote Workers
Just as with any technology deployment, you should have some objectives for enabling your remote workers with technology. In this guide you will learn:
✓ How to maintain productivity when employees can’t come to the office.
✓ How to maintain data visibility for management, collaboration, and backup.
✓ How to maintain security so that data and access to your IT systems are protected.
Looking for a specific topic?
-
1
Don't Send Anyone Home to Work Without a Plan
-
2
One Size Doesn't Fit All
-
3
Devices Used to Access Apps and Files
-
4
Access to Applications
-
5
Access to Data
-
6
Communication
-
7
Long Term IT Strategy
-
8
Infrastructure in the Cloud
-
9
Microsoft 365 (formerly Office 365)
-
10
Hosted Phone Systems
-
11
Focus on Productivity, Data Visibility, and Security
1. Don't Send Anyone Home to Work Without a Plan
Whether your employees are working from home in response to the pandemic or you want to implement a remote workforce as part of your business strategy, it’s important to have a plan.
Your people want to get their work done. If they don't have a plan for how they're going to access files or how are they’re going to get a hold of someone, they're going to figure out their own solution – and when they do, it's probably not going to be as secure as you want it to be.
Before you know it, you have company data spread throughout personal versions of Dropbox, Google Drive, flash drives, and who knows where else. All of these places are invisible to IT management.
When your data gets dispersed, you lose the control that you've carefully set up around the perimeter of your network. Now your data is EVERYWHERE. You can't back it up, you can't secure it, you can't control who sees it.
2. One Size Doesn't Fit All
It would be great if there were a formula you could apply to every single remote worker situation, but there isn’t one.
People in different departments, in different roles, have different applications and different needs for data access. Your particular IT environment and whether your network and data are in the cloud, on servers at your business location, or both will determine your approach to setting up remote access.
There are also regulatory compliance requirements to be considered in some industries. These requirements stipulate how data is controlled. You’ve carefully set up operations to make sure that you maintain compliance. Once you start taking people out of that environment, you could potentially lose control and that would immediately put you out of compliance, depending on how it's all done.
3. Devices Used to Access Apps and Files
Part of your remote worker strategy should address how employees will get to the applications and files they need. An equally important part is addressing what devices they’re going to use to do that.
Using company-owned and managed smartphones and laptops is obviously the best choice because the security parameters around your network extend out to those devices.
Ideal? Yes. Reality for many businesses? No.
There are a lot of businesses where laptops are not provided by the company. Now what do you do? It's unlikely that you're going to buy new phones and new laptops for every employee when you’re in the middle of a crisis, so you're probably looking at having people use their home computers and personal cell phones at least for the interim.
This will speed up the time it takes to get up and running, but there are security concerns you’ll need to address.

Concerns About Using Personal Devices for Work
When your employees use their own cell phones and computers for work, you don't know if:
- They have endpoint protection or other security software systems.
- Their operating systems are up to date.
- They're doing anything else on these devices that could pose security threats or if anyone else might have access to them.
If your only choice is to let employees use their own equipment, you may have to run scans to make sure the device doesn’t already have a virus or some other kind of malware that could be spread to your network.
For cell phones, you might want to include them in your mobile device management program.
Whether employees are working on company-owned devices or their personal computers and phones, you can still meet security requirements that allow employees to access applications and files, communicate, and collaborate so that they can get their work done.
4. Access to Applications
Your business probably uses a combination of common business software and industry-specific software. Getting people the right access will be important to their productivity.
Web-Based Software
If your business already uses web-based applications, then access is only dependent upon a device and an internet connection.
These cloud apps are often very specific to departmental needs, like Marketing or HR. Many Line-of-Business (LOB) software applications, such as ERP systems or time tracking software, are also now web-based, which will make it easy for your remote workers to pick up where they left off.

Email and Microsoft 365 (Formerly Office 365)
If you’re using Microsoft 365 (formerly called Office 365), your email is already available from the web too. It’s a little different than opening up Outlook on your PC, but moving to the web-based interface has a minimal learning curve.
Microsoft 365 can actually give you all your favorite Office programs through the web including some that you’ve probably never heard of.
Non-Web-Based Software
If you have software on servers at your business location, it’s going to take some detailed planning to get workers access.
The good news is that you can provide an experience that exactly mimics how they normally work at the office.
5. Access to Data
Once you know what applications workers need to do their job, they need access to data. Getting access to data might be easy if they’re working in the cloud – not as easy if the files are stored somewhere else. It’s very likely that you have a hybrid situation set up where part of your data is in one or more cloud locations and the rest is on servers at your business location.
File sharing applications like Dropbox and Box have some pretty robust collaboration and synchronization capabilities. Make sure that any file sharing app your people use is the Pro/Business version and not the consumer version.
Now that you know what devices your people are going to use, the applications they need, and where the data that they need is located, it’s time to put it all together with a remote desktop and VPN.
Remote Desktop
Accessing your office computer or other devices from any location using Remote Desktop Protocol (RDP) is just like using a remote control from another computer.
Remote desktop allows your employees to log into the computer that is physically sitting at their desk or a terminal server that you may have set up for them to log into, remotely.
Some great benefits of using a remote desktop are:
- Works with a Mac or PC.
- No need to install software on the device they’re using.
- Nothing is pulled over from your server.
The great thing about remote desktop technology is that employees can work exactly the same as they do in the office because, depending on how it's set up, it IS the same as if they were sitting in their office. It’s also really easy to set up if you're already using remote desktop for some employees. In a lot of cases, it can be easily expanded to include more people.
There are some secure ways to use Remote Desktop and there are some not-so-secure ways. It all depends on the setup, so make sure that your IT team isn't just opening up firewall ports to create the access needed for remote desktops. Doing so creates a pretty serious security vulnerability that will increase your risk of a cyberattack.

Virtual Private Network (VPN)
The way to use remote desktop securely is through a virtual private network (VPN). This is a technology that creates a secure tunnel between the computers that are talking to each other – that is, the computer in the remote location and your server. It encrypts the data that's moving back and forth, making it impossible for someone to “eavesdrop” on your communications or to intercept your internet traffic.
It will have to be configured, and it’s important to note that using a VPN still requires other security layers, such as single sign-on, firewalls, and endpoint detection and response (EDR). VPN isn’t a replacement for any layer of technical security – it’s an additional recommended layer.
Internet bandwidth also needs to be considered since VPNs use the bandwidth at your office. Do you have enough bandwidth to handle the additional traffic?
Think of it this way: Previously, you had people accessing apps and data physically at your office through your internal network. Now, they’re using the internet to get to those same resources.
It will take some planning to know if you have the appropriate bandwidth to support the increased internet traffic and to figure out how you can segment the traffic for optimal performance.
6. Communication
Voice Communications
Once the workplace gets dispersed, there's going to be a culture shift in communication. Simple, but important, questions like “Who's going to answer the phone?” and “How should employees communicate?” need to be considered.
If you have a VoIP (Voice over IP) system, then this is easy. If you don’t, you’ll have to figure out exactly what capabilities you do have and how you can use them. For example, you may be able to forward calls to cell phones, but calling out will be a little different. It may confuse people because the phone numbers won’t be consistent.
Your business phone system greatly affects your ability to provide a seamless communication experience for your employees, customers, and vendors.
Collaboration Tools
Working remotely is lonely sometimes, especially if you haven't done it before. Having collaboration options available to your team will keep everybody connected.
Technologies such as Microsoft Teams, Zoom, GoToMeeting, etc. enable your staff to still have a personal connection when they're not physically next to each other. Sometimes when you're communicating solely via email or a text-based communication, you lose a little bit of that connection and human side of things, but with video calls you can chat like you’re right there with them.
Instant messaging software is a great internal communication tool. Again, programs such as Microsoft Teams, Zoom, and Slack are going to be helpful to get the quick answers that you might need when people are used to working together.

7. Long-Term IT Strategy
You might be reading this because you’re trying to quickly pull together a remote working solution, or maybe you've already partially addressed how technology is going to help you come back from an emergency in your business continuity plan.
Whatever your situation, there are plenty of ways that you can be thinking through how enabling remote workers is going to be a strategy moving forward.
Evaluate Resources and Home Network Capabilities
A good first step would be to survey employees and figure out who can work from home if needed.
Ask who has things like:
- A quiet, secluded place to do uninterrupted work
- A PC or laptop
- Reliable high-speed internet
- A microphone, speakers, and a webcam
- Dual monitors, if needed
- Whatever else your employees may need to be productive from home
These are just a few things to help you evaluate those on your staff who are physically able to get set up to work at home.
On the IT side of evaluating remote work capabilities and setup, it’s important to understand that every home environment is different. Some can be set up more easily than others. For a lot of smaller organizations, IP schemes can actually be the same on a home network as they are on a business network.
Once you get to a certain point, you may run into a challenge where it's going to take a significant amount of time just to get a home network set up to VPN into the work environment. In that case, you may need to find a different solution.
Get IT Guidance Before Making Decisions
One thing is for sure - talk to your IT team ASAP if you’re considering sending employees home to work. The speed at which your plan can successfully get rolled out is based on what you currently have.
In some cases, a bare-bones SECURE setup can take one or two hours per user. Multiply that by 10, 20, or 50 users…and it might be a while before everyone is up and running.
Whether you have a formal IT strategy or not, the goal of enabling remote work is to make your organization resilient so your business can continue without major disruption from a workflow perspective. Whether you’re facing a public health threat, a natural disaster, a regional catastrophe, or some other type of business disruption, enabling remote work can mean the difference between carrying on or shutting down.
8. Infrastructure in the Cloud
Moving your infrastructure to the cloud can be a way to gain resilience and scalability at the same time.
By infrastructure, we mean that all your applications and data are on a server somewhere outside of your physical business.
Resilience comes from alleviating concerns that equipment might be damaged in the event of a local disaster, and you’ll gain the ability to access your systems from anywhere.
Scalability comes from the ability to increase capacity without buying new equipment.
Deciding to move to the cloud is complex and involves many areas of evaluation including:
-
Will there be differences in functionality that will affect your workflow?
-
Do you have adequate internet bandwidth to handle increased traffic?
-
How will you secure all the endpoints and connected devices?
-
Is moving to the cloud a good idea financially? (Subscription vs. capital investments)
-
What is your plan for data backup and disaster recovery? (Yes, you still need one!)
-
How will you support users and facilitate changes with your cloud vendor?
Benefits of IaaS (Infrastructure as a Service)
While the conversation about moving your infrastructure to the cloud is complex, there are many benefits to be reaped when this fits into your IT strategy including:
- Cost-effective alternative to purchasing servers and other hardware.
- You may end up with an increased level of security.
- Flexibility when you need more or less capacity.
- Accessibility from anywhere there’s a secure device and adequate internet.
- Enhanced collaboration when your team is spread across multiple locations.
- Resilience in the face of a crisis or disaster.
As you’re considering moving your infrastructure to the cloud, you should also be thinking about what kind of technology experience you want for your employees and customers. If IaaS helps people serve customers in ways that are faster and better, then IaaS could become your competitive advantage.
9. Microsoft 365 (formerly Office 365)
We’ve already briefly mentioned Microsoft 365 when we were talking about your applications. It’s true that a lot of people think of Microsoft 365 as just a way to get their email, which it is and that's great, but it is so much more than just an email replacement. It gives you a ton of useful apps in one subscription.

Teams
Teams is an all-in-one communication app. At VC3, we use Teams daily for video calling, instant messaging, and meetings. We use it each month to livestream our all-hands meeting for those who can't be at the office physically. And we've even replaced our office phone system with Teams.
Stream
Stream is another app to highlight in Microsoft 365. Stream acts like a digital library where you can catalog training videos, meeting recaps, videos that had been created internally, and just about anything that you want to give people access to on a continuing basis.

SharePoint
SharePoint is another useful Microsoft 365 app. It’s an online file storage and sharing platform, but it also helps with collaboration. People can edit documents together in real time without getting that annoying message saying somebody else has to close it before you can get into it.
You can set up different workflow approvals as well as multiple checkpoints to keep track of progress. You can even control access for different people and/or roles, which is important for sensitive documents and information.
There are many more cool things you can do with Microsoft 365 apps. These are just a few of the apps that are included with some subscriptions. There are varying levels of subscriptions based on what your organization needs.
10. Hosted Phone Systems
A crisis situation is not the time to switch out your whole phone system, but it’s probably a time when any inadequacies that you’ve been living with will show up as big obstacles. Communications are absolutely imperative for business operations in good times and bad, and upgrading your phone system to VoIP (Voice over Internet Protocol) should be included in your long-term IT strategy.
VoIP is essentially a digital phone service that travels over the internet. The software to run the service is in the cloud, so you don’t have to buy and maintain any equipment. You do need to have adequate internet bandwidth because of increased traffic, but the good news is that in many locations fiber connections have made that a lot easier to get.
Unified Communications With VoIP
Today’s phone systems are packed with capabilities that make connecting, communicating, and collaborating easy and fast. Want to get your calls on your cell phone or your laptop? No problem. Want to switch from a call to a video meeting? Easy. Want to speed up response time of your internal teams with messaging? Piece of cake.
A modern phone system will make enabling your remote workforce with communications a consistent experience for employees, customers, and vendors.
Some other benefits of VoIP phone systems include:
- Lower costs that you can categorize as an operating expense instead of a capital expense.
- Integration with your business applications like Microsoft 365 and your CRM.
- The ability to scale your system up or down according to changing needs.
- Improved responsiveness and customer service.
- Ability to support multiple business locations as well as a remote workforce.
Choosing the Right Phone System
There are many different factors that go into choosing the right phone system, starting with business needs. It’s also vital to think about how new phone technology is going to work with your current network, and if you need to make other changes – like getting more internet bandwidth – to realize all the advantages that the vendor promises.
11. Focus on Productivity, Data Visibility, and Security
When you’re enabling remote workers with technology, having a plan that focuses on productivity, data visibility, and security will be important to your success.
Think through:
- What devices people are going to use
- What applications they need
- How they’re going to get their data
- What is the security strategy
- Determine if you have enough internet to make it all happen
Bottom line: Make a plan for when/if people have to work from home.
Where to Start
Start your planning by surveying your employees to figure out who might already be set up to work from home if needed.
Here are a few questions to ask:
- Does the employee have a home office (a quiet, secluded space for uninterrupted work)?
- Are they working from a PC or laptop?
- How reliable is their high-speed internet?
- Does their PC or laptop provide for a microphone, speakers, and webcam?
Next, talk with your IT team about your goals. They’ll help come up with a solution that meets your budget and timeline for implementation.
We're Here to Help
There are many steps that you can take with technology today that are going to help you to be resilient regardless of a regional catastrophe, weather disaster, public health threat, a fire nearby that cuts your power, etc. Preparing a plan for them is the right step in keeping your business operations rolling as productively and securely as possible.
If you think your organization might need help with the remote work plan development, a security assessment, or just an honest second opinion on your situation - we are here and happy to help.
Fill out the form below to schedule a free consultation.